The concept of a “dark archive”
The Technische Informationsbibliothek (TIB) – German National Library of Science and Technology operates what is known as a “dark archive”, and by doing so pursues the concept of separating the archive from the search function:
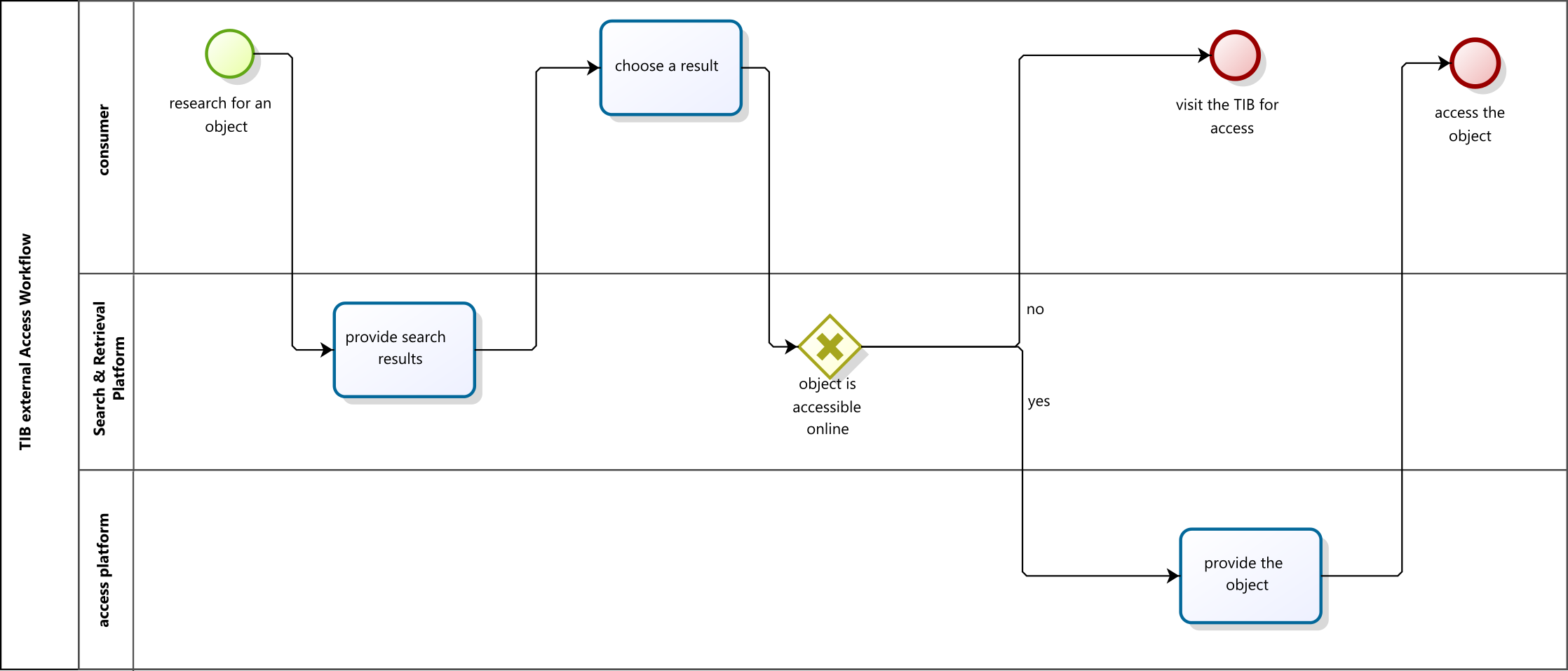
- Users have no direct access to the objects in the digital preservation system. TIB’s collections are available on the TIB Portal as well as on other access platforms.
- Users never search directly within the digital archive; searches always take place via a presentation platform.
The Rosetta digital preservation system has interfaces that can be used to connect presentation platforms to Rosetta. When searching on the presentation platform, the user may call up a link in the record that refers to the access copy stored in Rosetta.
Even now, TIB configures different access rights for each object, which regulate access to the access copies. These access rights are recorded as Access Right Policies, and documented in the METS file. The access terms regulate which authorisations are required in the case of distribution in order to have the permission to use the object.
Other access rights, such as limiting the number of simultaneous accesses, can be configured at any time, as required.
Roles and access authorisation
A role assignment scheme governs staff access to objects. Every role stipulates different levels of authorisation: view, edit and delete rights. The requirement is that users only receive the roles and rights immediately required for their work.
The three German national specialist libraries operate the digital archive collectively. The system is client compatible, enabling each institution to have and edit its own area, for which it is responsible. Irrespective of their role and authorisation, employees may only search and access their own institution’s objects in the digital preservation system. TIB is responsible for the administration of the overall system, and is authorised to do so. Principles relating to overarching tasks and the demarcation of responsibilities are stipulated in a Consortium Agreement.
Access scenarios
User access
TIB currently operates a dark archive; users do not access the objects archived in Rosetta; they use various access platforms to access them.
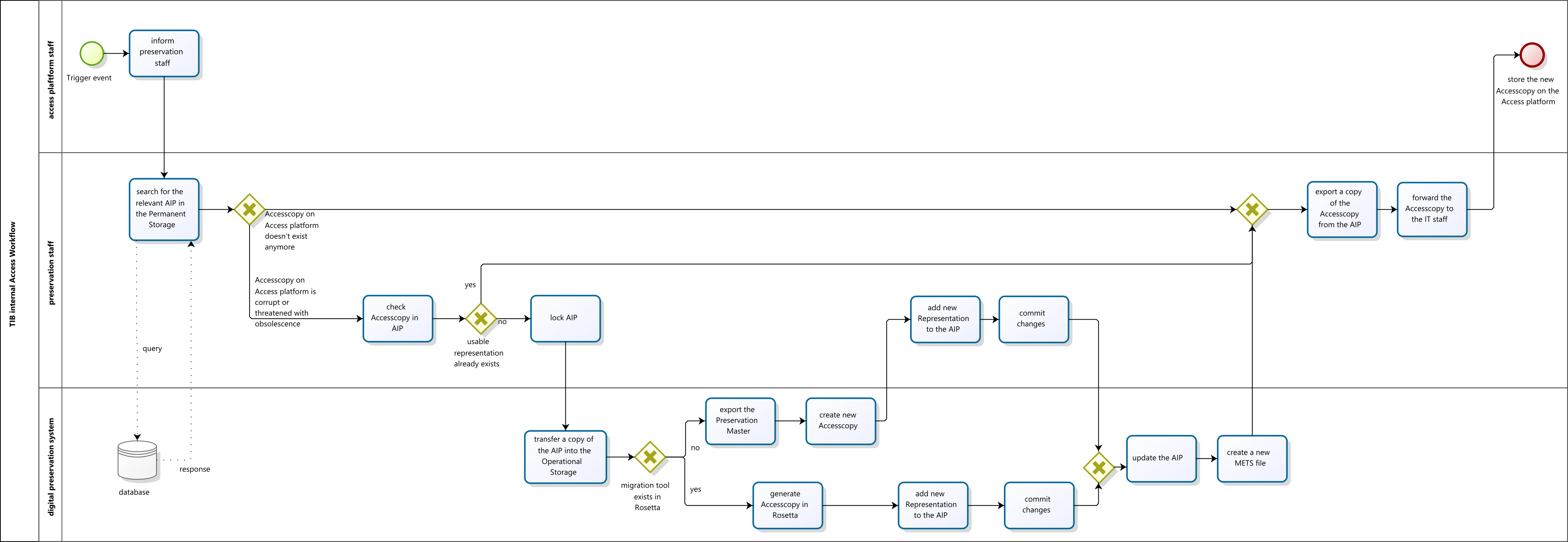
Access by authorised staff
During the ingest of objects, the digital archive imports existing access copies from access platforms as DERIVATIVE COPIES in the digital archive, and transfers them back to the access platform in the case of a trigger event. Trigger events are:
- The access copy no longer exists on the access platform.
- The access copy on the access platform is corrupt.
- The access copy on the access platform is at risk of obsolescence.
If an access copy is no longer legible, this is reported to the digital archive by the body responsible for the access platform in question.
Access scenarios are documented in the form of process diagrams.
Process diagram: User access
Process diagram: Access by authorised staff
Click to enlarge